The AML CTF Program Built for Australian Compliance
From building your AUSTRAC-aligned program to specialist-led risk reviews and more, Visibl is a total system for helping to manage your AML CTF compliance program. We combine the speed of AML compliance software with the certainty of local experts so your business is always protected.

Everything you need for your anti money laundering compliance program
Everything you need for your anti money laundering compliance program



Assess risk and build programs without expensive consultancy.
Assess risk and build programs without expensive consultancy.
We’ve translated Australia’s 88-page AML legislation into a smart online risk questionnaire tailored to your industry and business. Simply answer a series of guided questions about your customers, services, transactions and operations, and we'll help identify any risks and potential controls. This creates your risk baseline, the foundation of your AML/CTF compliance program. Inside the platform you’ll then have your policies, procedures, controls and roles required to manage those risks, all captured in one system with a clear audit trail. With the speed of purpose-built AML software and the reassurance of certified specialists when human judgment is needed, Visibl delivers the best of both worlds.
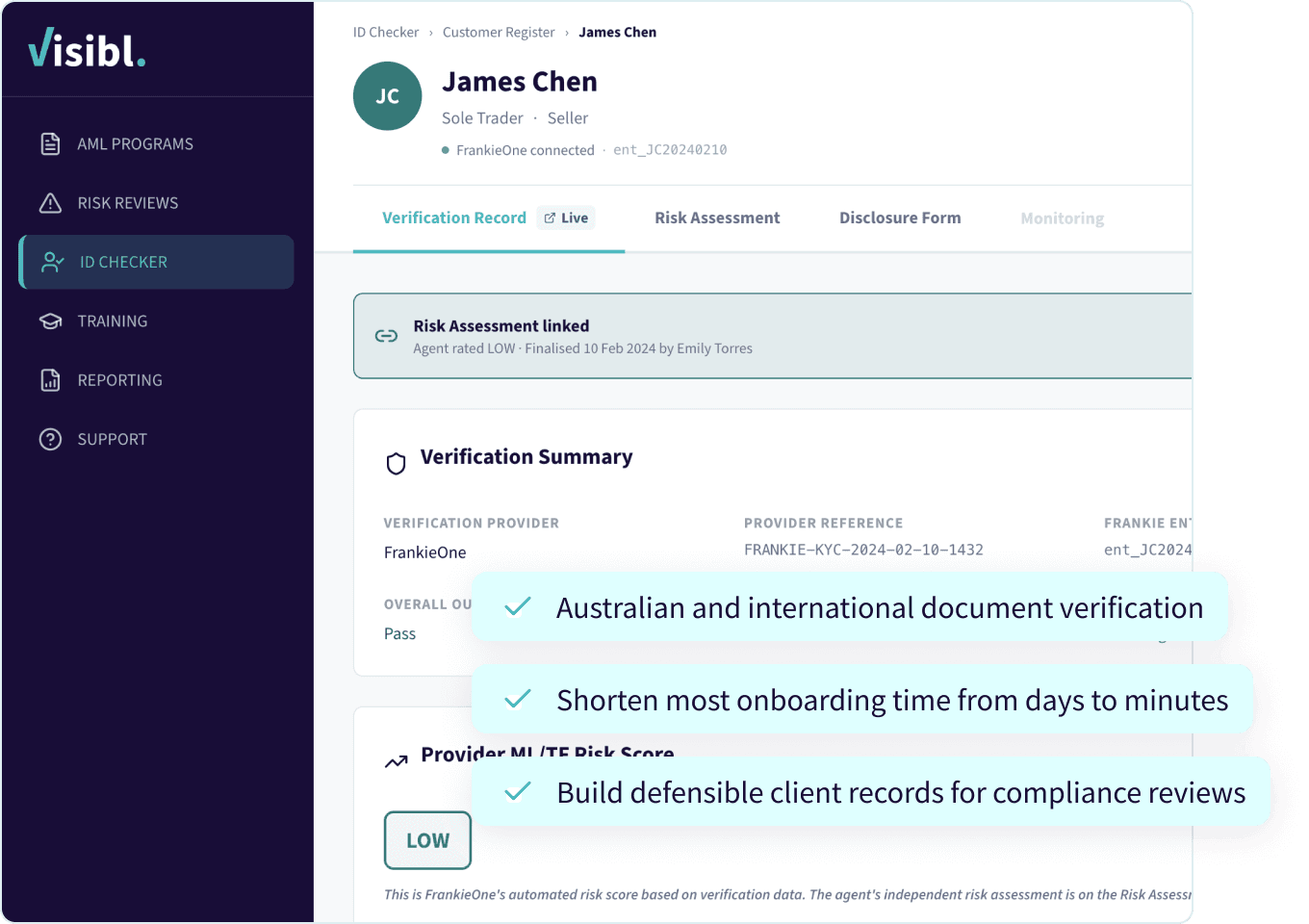
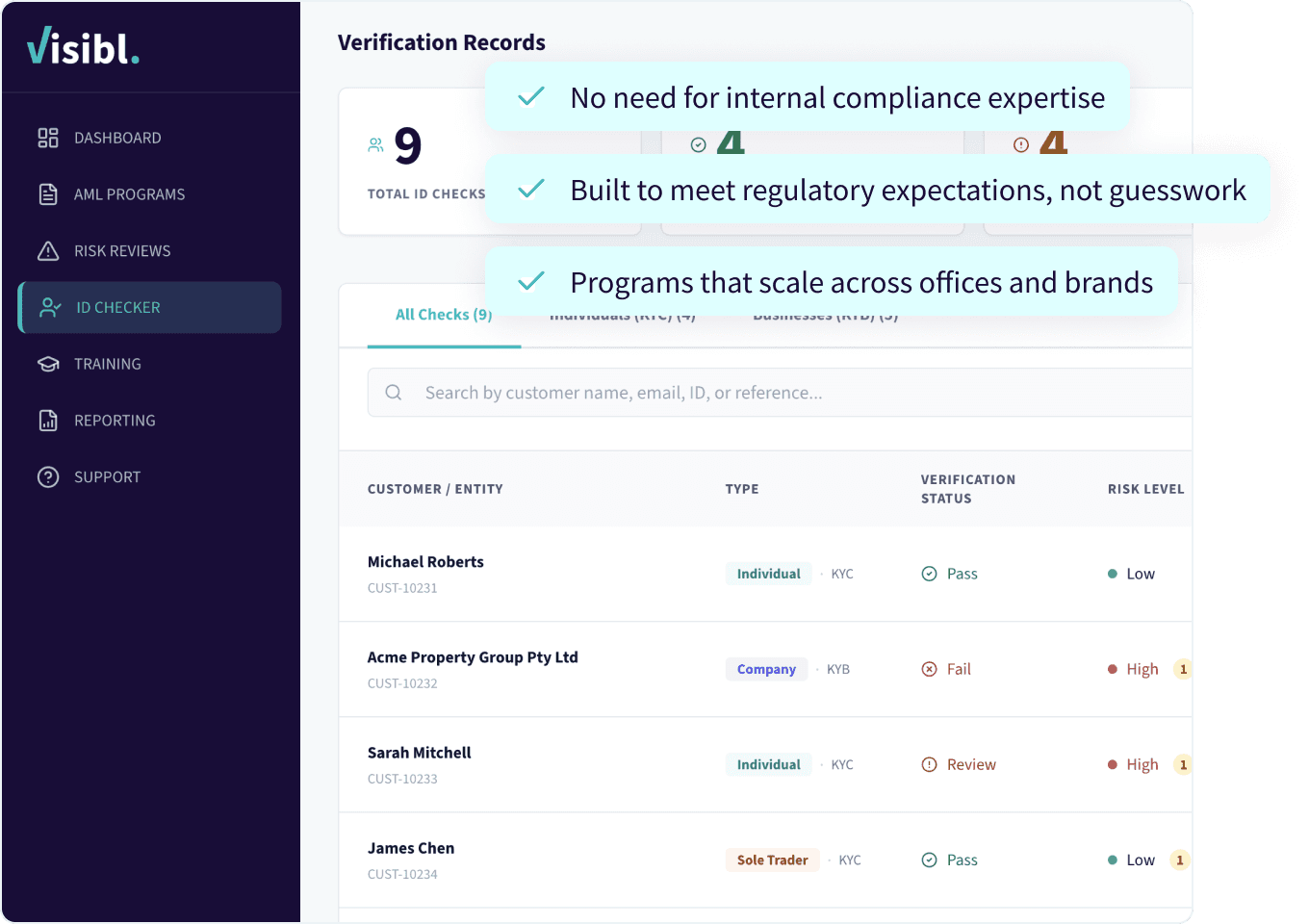
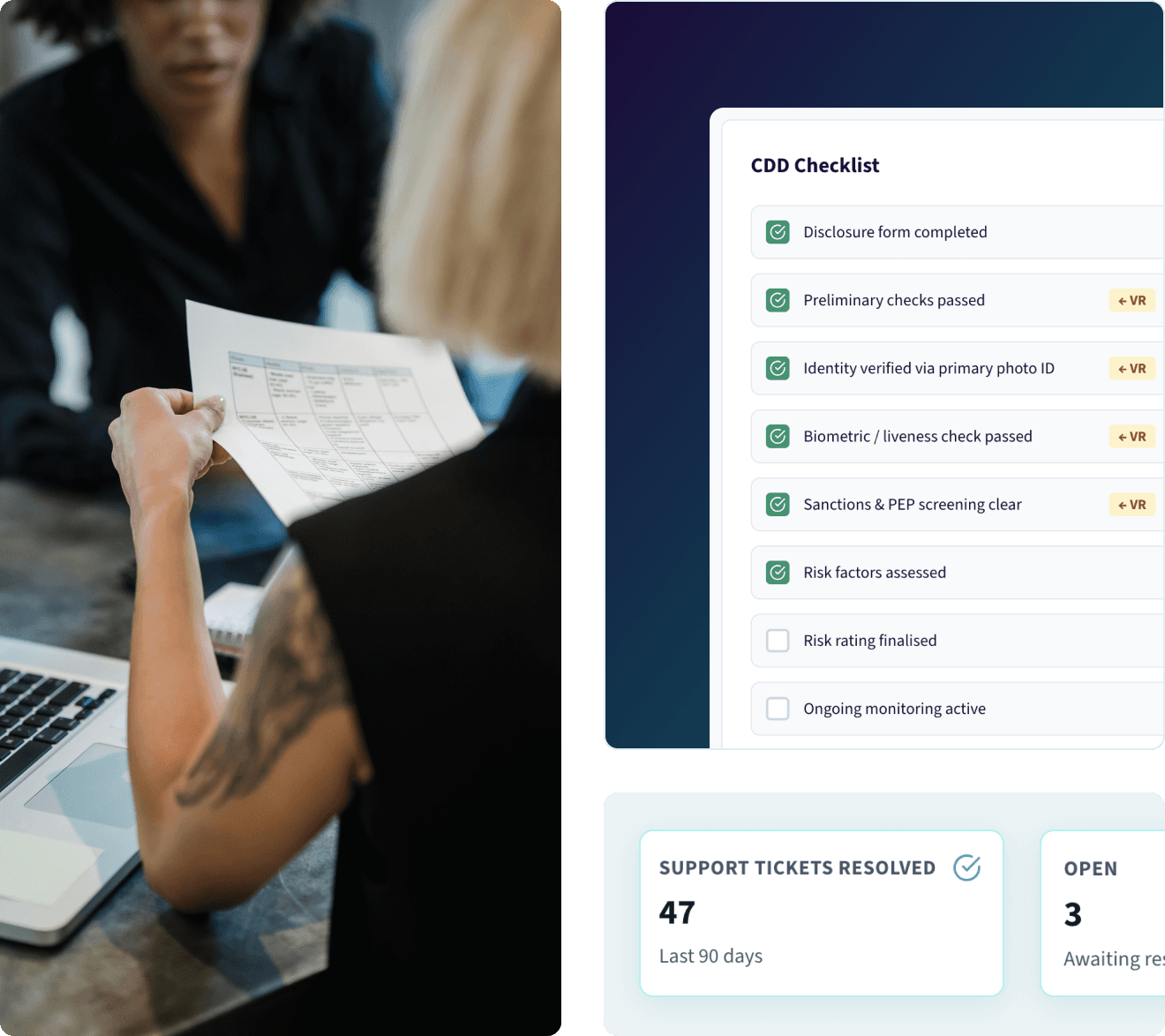
Secure, fast digital onboarding and verification.
Secure, fast digital onboarding and verification.
Visibl connects into a global ecosystem of verification tools trusted by top Australian banks and financial services companies. With access to over 350+ data sources you’ll get fast pass rates making it quick and easy to onboard more buyers and sellers. We’re confident for domestic checks you’ll enjoy straight-through verification 95% of the time and for the other 5% Visibl Consultants can guide you through exactly what documents to collect.
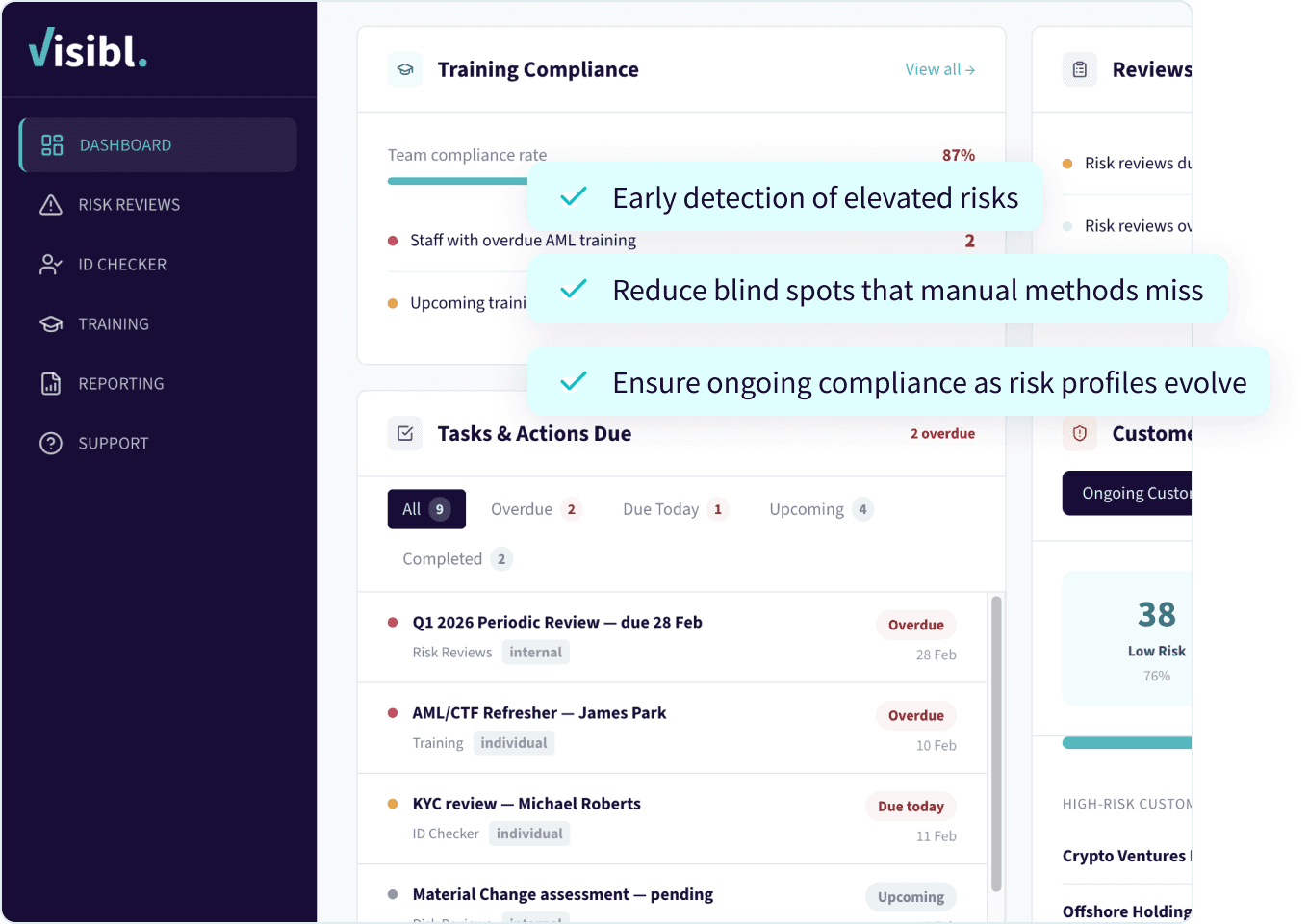
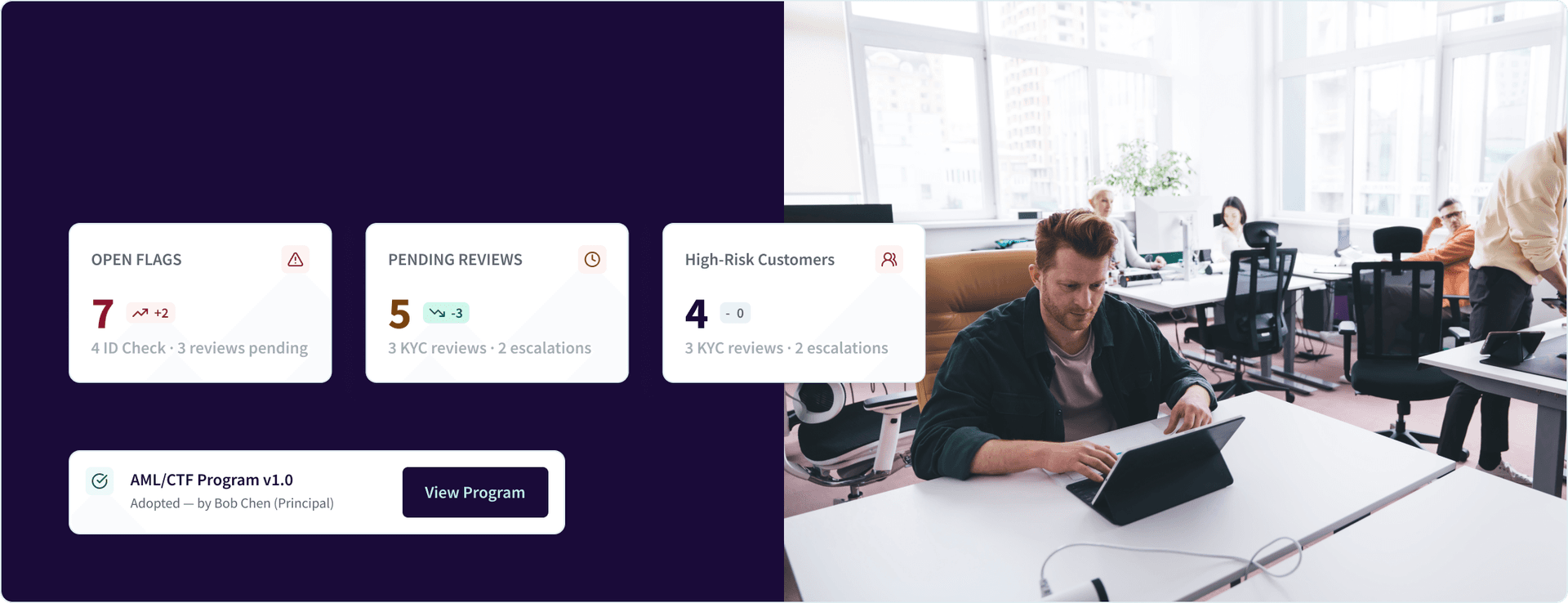
Maintain oversight without manual tracking.
Maintain oversight without manual tracking.
Changes in business are expected, and having visibility and tracking of them means your compliance program evolves with the needs of your business. Under the new AML regulation you’re obligated to report material changes to AUSTRAC, with Visibl you can easily and simply log the change and submit to AUSTRAC in the format they expect.
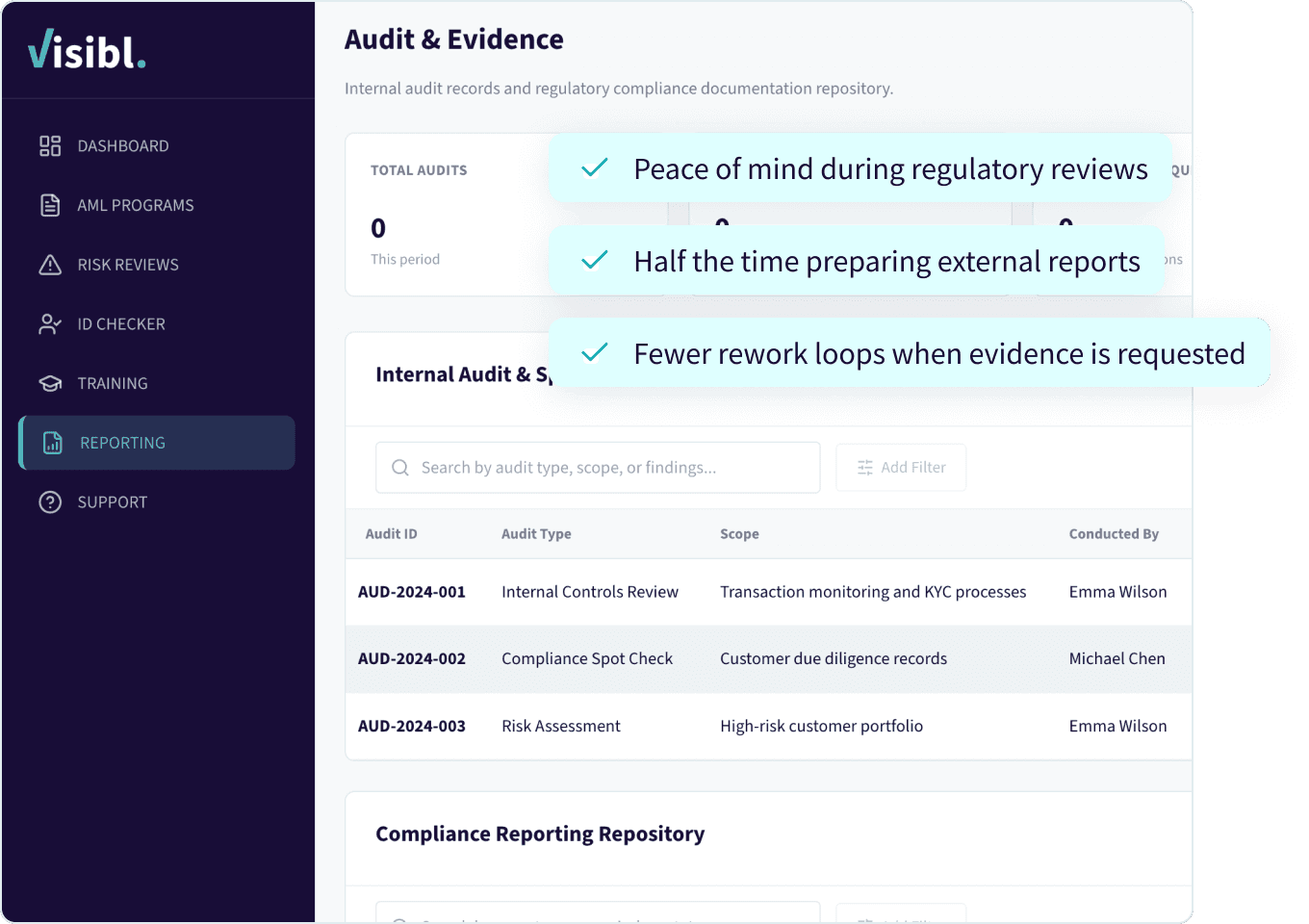
Audit-ready capture, storage and reporting
Audit-ready capture, storage and reporting
When it comes to submitting your first compliance report (due 31 March each year) you can be confident we’ve taken all the questions out of the AUSTRAC compliance report, structured them into the Visibl platform, and then pre-populated the report using the information you’ve tracked over the prior 12 months. So when you log into AUSTRAC you’ve got a ready-made report structured exactly as they require, you just hit submit.
Certified AML experts where you need them
Certified AML experts where you need them
How it works:
Specialists help set up your ML/TF risk assessment, AML/CTF policy
Review documentation and risk decisions
Advise on verification escalations, complex UBO structures and edge-case scenarios
Provide interpretive support throughout compliance lifecycle
AML Supplementary live training available

True defensibility — not just automation

Reduction of compliance anxiety + personal liability

Internal team capability uplift
Standardisation and control for all your offices
Standardisation and control for all your offices
Equip your team with the right compliance knowledge
Equip your team with the right compliance knowledge
Enterprise-grade security designed
for sensitive compliance data
- Protect client & business data with confidence
- Maintain records for 7 years

Encrypted storage and transmission

Audit logs for all activities

Role-based access controls

Secure identity and verification flows

“Coming from banking I understand working in a regulated industry but I wasn't exactly clear on the level of reporting obligations for us as a buyer’s agent under Tranche2 compliance. The demo with Visibl was tremendously helpful and clearly translated an 88 page document for me precisely for my industry and our business.”
Eshanee Collins, Settlement Coordinator, InvestorMate
Austrac Tranche 2 reforms expand Australia’s AML laws to cover a range of professions such as real estate agents, buyers agents, corporate service providers, lawyers and accountants. Learn how Visibl supports all.
Austrac Tranche 2 reforms expand Australia’s AML laws to cover a range of professions such as real estate agents, buyers agents, corporate service providers, lawyers and accountants. Learn how Visibl supports all.
Your margins shouldn’t have to absorb compliance inefficiency. Visibl helps your firm meet Tranche 2 expectations without slowing deals, hiring specialists or building internal compliance teams.


